
SPECIAL ARCSI CRYPTOLOGY EXHIBIT
Association des Réservistes du Chiffre et
de la Sécurité de l’Information (ARCSI.FR)
Notice: Only on October 24, 2018
Perfect mastery (or ignorance) of cryptology, is at the origin of many successes and failures, that have greatly altered the course of history. For example, the decoding of the Zimmerman Telegram, which drew the USA into WWI, Georges-Jean Painvin decipherment of German cipher ADFGVX and the radiogramme de la Victoire.

Georges Jean Painvin cryptanalyste deciphered ADFGVX WWI
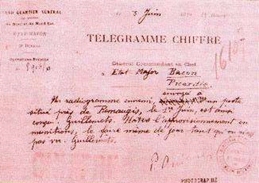
"Télégramme de la Victoire"
Also the Polish, French, British and US cooperation for decryption of German Enigma machines, 1932-1945, which helped to shorten the Second World War by about two years and saved untold numbers of lives. Until the 1970s, cryptology was held secret by most governments of the main victorious nations. Research, machines and software were classified top secret, and known only to a few insiders.

WWII German Enigma machine
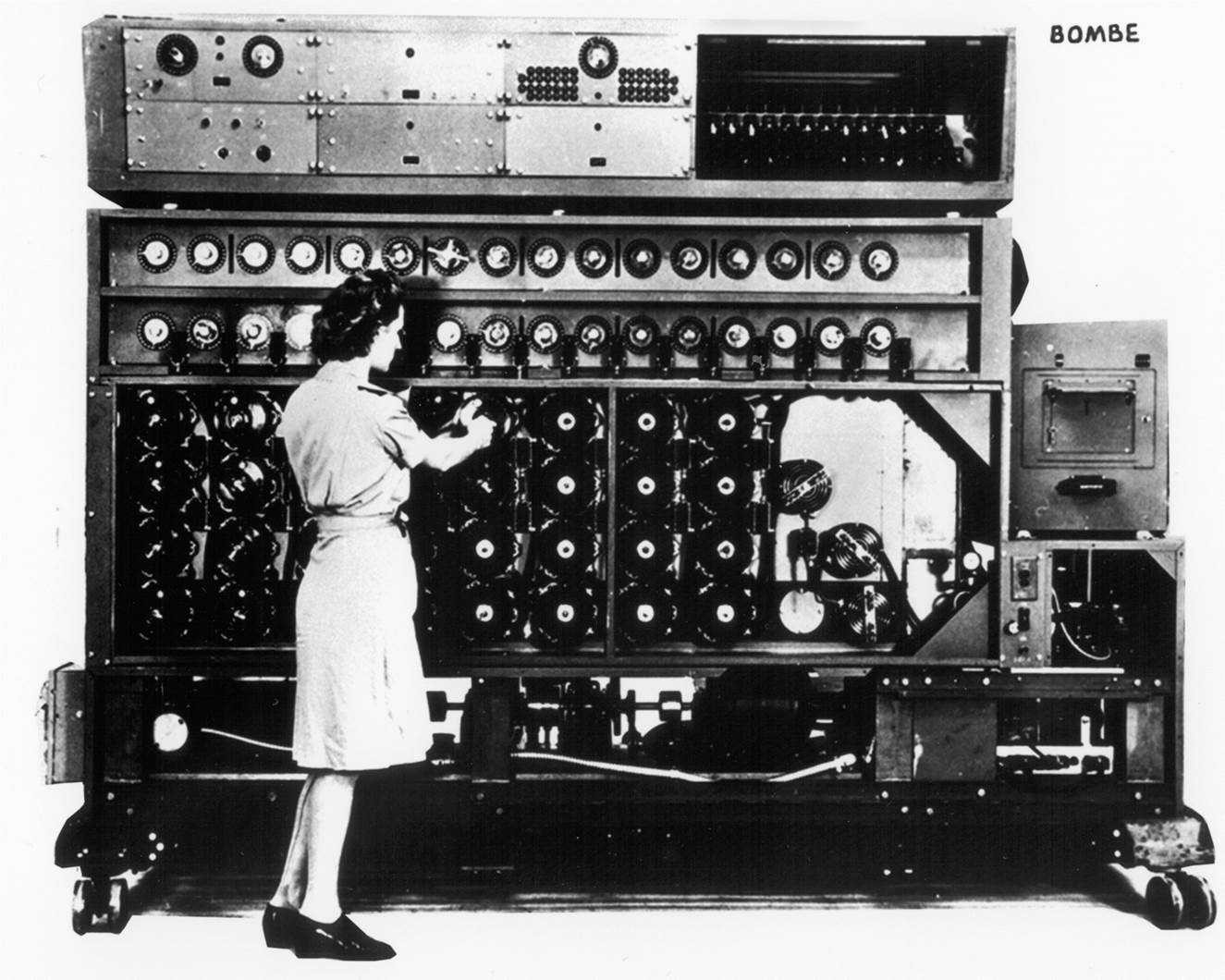
British WWII Bombe to find Enigma keys in 20 minutes
Today, Cryptology is constantly used everywhere, in our digital, cyber and mobile universe, for instance, the security of electronic transactions, protection of digital media and bank accounts, and more recently crypto-currencies. Cryptology and information security are now revolutionized with block chain technology and quantum cryptology.
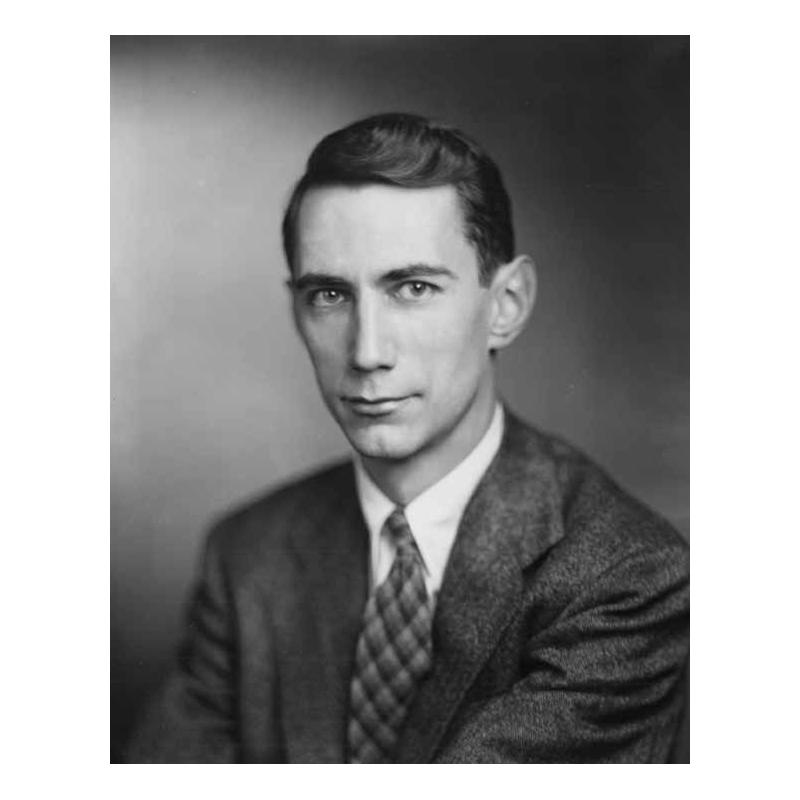
Claude Shannon, founder of Information theory
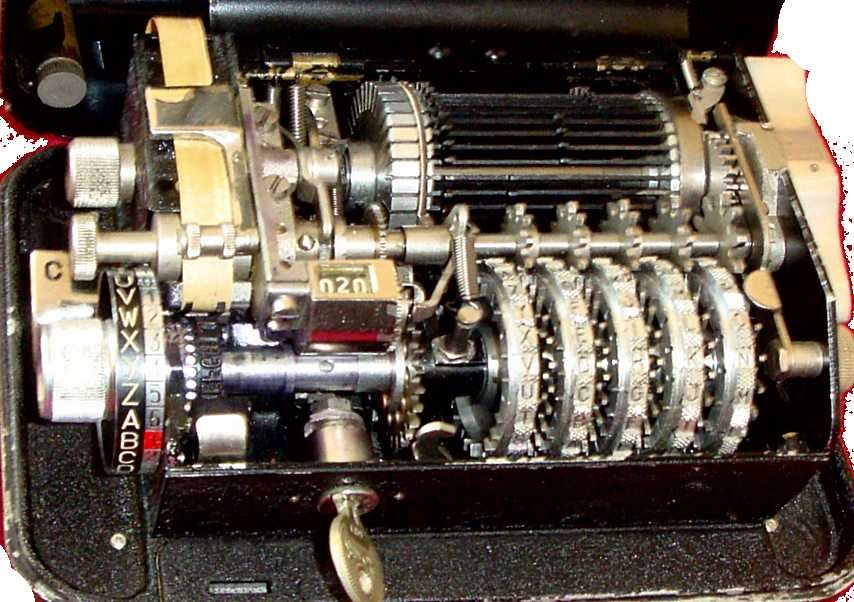
1936 Hagelin C-36 French Cipher Machine
ARCSI proudly presents a part of its material and heritage accumulated since 1928. We display the 3700 years of history, personalities, machines and techniques, seen previously in the shadows and without recognition. ARCSI members will demonstrate little known mechanical cipher machines, from 1930s – 1970s, and also a pocket sized Enigma simulator and a reconstructed part of a famous top secret WWII Speech encryption system, SIGSALY, as discussed in the CSNET keynote speech.

ARCSI Enigma Simulator

SIGSALY 1942 reconstructed Quantizer
Our exhibit will inform and open new perspectives to the conference attendees, and to the next generations of information security and cryptology experts. We hope that it will bring you into this fascinating world of secret codes, cipher software and hardware.
Key dates
- Paper Submission Due
May 13, 2018May 23, 2018 (Firm) - Paper Review Feedback
July 2, 2018 - Final Papers Due
July 15, 2018 - Conference
October 24-26, 2018







